VoltPillager: Hardware-based fault injection attacks against Intel SGX Enclaves using the SVID voltage scaling interface | USENIX
Hardware-based attacks based on different entities in the semiconductor... | Download Scientific Diagram

Electronics | Free Full-Text | An Extendable Software Architecture for Mitigating ARP Spoofing-Based Attacks in SDN Data Plane Layer

Hardware security knowledge in terms of the hardware-based attacks,... | Download Scientific Diagram

A survey on physical unclonable function (PUF)-based security solutions for Internet of Things - ScienceDirect
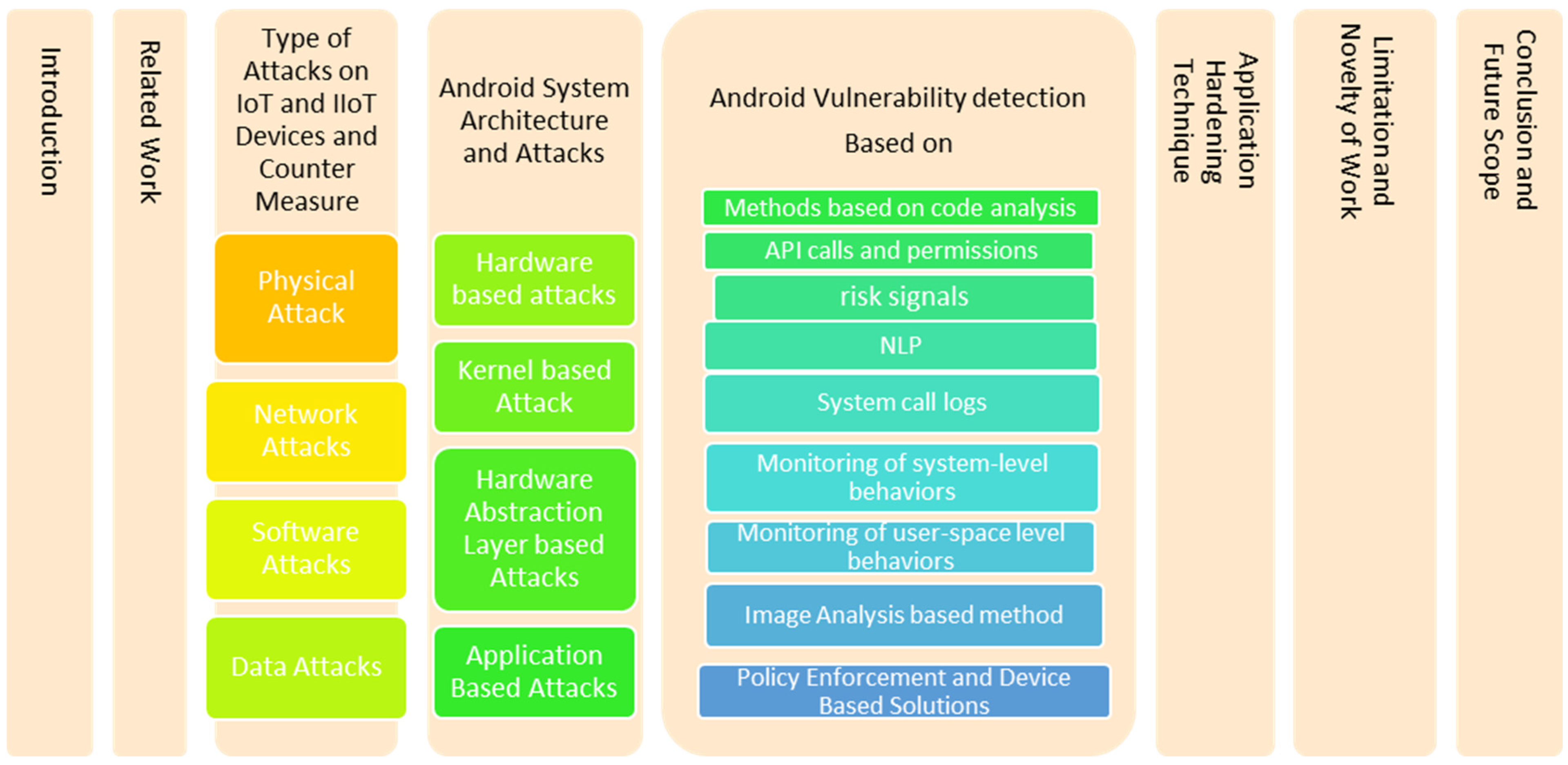
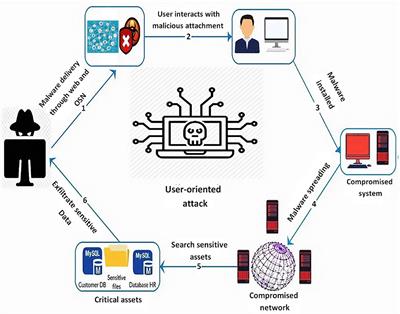
Electronics | Free Full-Text | Malware Analysis in IoT & Android Systems with Defensive Mechanism

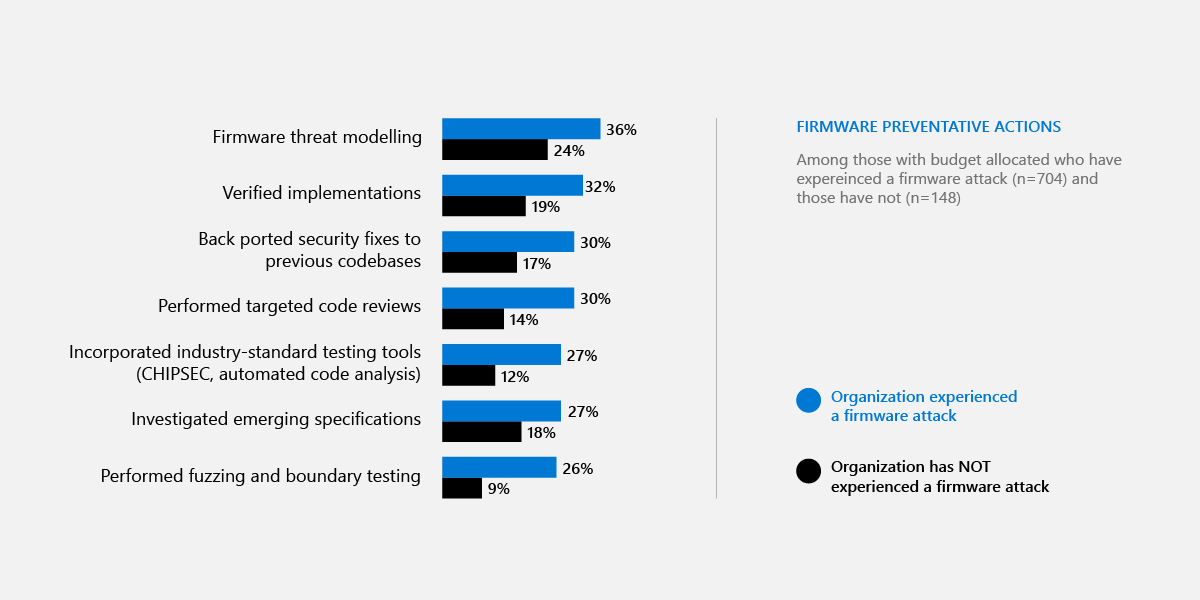
Hardware security knowledge in terms of the hardware-based attacks,... | Download Scientific Diagram